Chain of custody is not just a technical term; it is the documented, chronological trail that tracks an item from the moment it comes into your possession until its final disposition. For any operation handling sensitive materials, this process is the bedrock of proving an item’s integrity. It creates a verifiable, unbroken history for every single asset, ensuring accountability at every step.
Why Chain of Custody Is More Than a Paper Trail
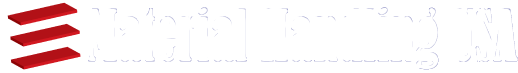
When most people hear “chain of custody,” their minds jump to courtroom dramas and forensic labs. While that is a major application, the reality is that these procedures are the operational backbone protecting your most valuable assets, no matter what industry you are in.
A documented, unbroken timeline is non negotiable for everything from high value inventory and irreplaceable lab samples to critical evidence.
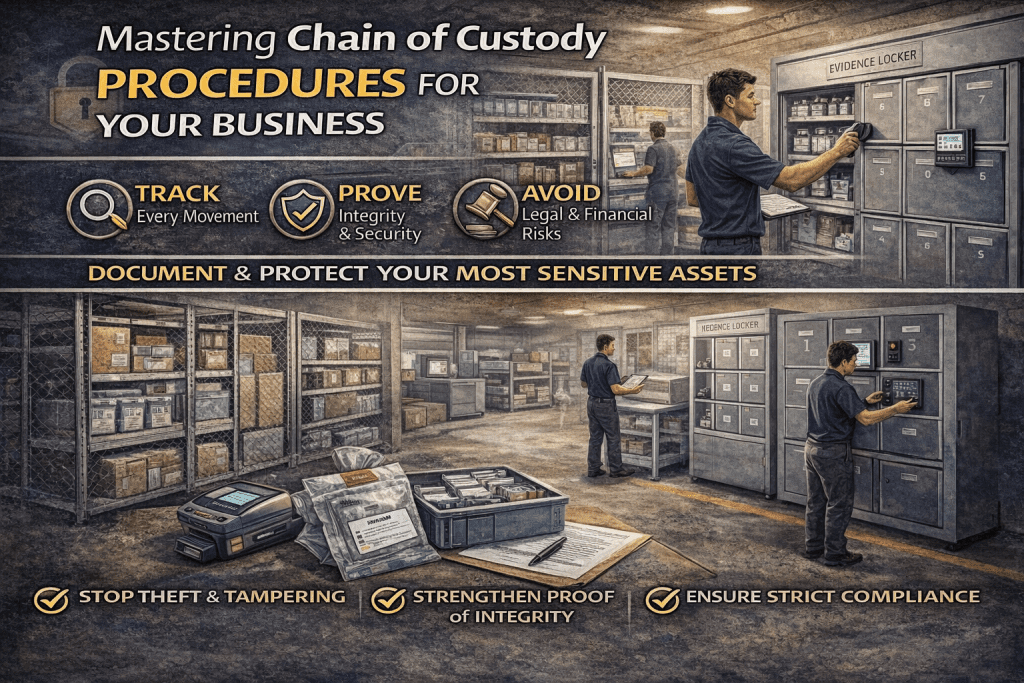
Imagine a pallet of high end electronics vanishing while in transit. A broken chain of custody means far more than just lost product. It is lost revenue, a hit to your reputation, and a cascade of potential legal headaches. These procedural gaps are where massive financial and operational risks hide, making robust chain of custody procedures a strategic necessity, not just a compliance checkbox.
The Foundational Role of Physical Security
Let’s be clear: a paper trail is only as reliable as the physical environment protecting the assets. An effective chain of custody depends just as much on physical security as it does on meticulous documentation. Secure storage is your first and best line of defense against tampering, theft, or contamination. This is where your operational integrity truly begins. With our fastest shipping in the industry, you can secure your facility quickly.
Key physical components that form this foundation include:
- Evidence Lockers: These give you individual, secure compartments for high value or sensitive items. Access is tightly controlled at every stage of handling. You can find more details in our comprehensive guide to evidence storage.
- Security Cages: For larger items or bulk storage, wire security cages are a formidable barrier. They keep things visible but prevent any unauthorized hands from getting near them.
- Controlled Access Points: Simply limiting who can enter storage areas and when is a fundamental control measure. It is a simple concept that reinforces the entire system.
The Growing Importance in Modern Operations
The need for strict, clear protocols is only growing. As supply chains get more complex and research becomes more advanced, the integrity of every sample, component, or piece of evidence becomes even more critical.
Yet, you would be surprised how often standardized guidelines are lacking in the field. A literature review spanning from 2004 to 2022 found only 105 articles in a major database that specifically addressed chain of custody in forensics. You can see these findings on chain of custody research here. This research gap underscores just how vital it is for organizations to establish their own clear, robust, and defensible procedures to protect their operations.
Building Your Chain of Custody Framework
Moving from theory to a system that actually works means getting practical. A solid chain of custody procedure is built in stages, starting from the moment an item enters your facility all the way to its final disposition. This is not about adding bureaucracy; it is about creating a repeatable, standardized system that slashes human error and ramps up accountability.
The first move is to establish a secure intake point. This is your controlled gateway where every single item is officially received, inspected, and entered into the system. Think of it as the formal start of the item’s documented life under your care. Without a clear intake process, items can get lost or misidentified before they are even logged.
Standardizing Intake and Labeling
As soon as an item arrives, it needs a unique identity. Implementing crystal clear labeling and tracking protocols is non negotiable. This is where quality barcoding supplies become invaluable, allowing you to assign a unique identifier that can be scanned and tracked electronically throughout its entire journey.
At a bare minimum, every label should include:
- A unique case or item number
- The date and time of collection
- The name of the person who collected it
- A brief, clear description of the item
This initial data entry creates the very first link in the chain, giving you a solid foundation for all the tracking that follows. It wipes out any ambiguity and ensures everyone is working from the same script.
The risks of a broken chain of custody are serious. As the flow chart below shows, a single lost asset can quickly snowball into lost revenue and major legal exposure.
This visual makes it painfully clear: a procedural failure at the very beginning can have severe financial and legal consequences down the line.
Documenting Every Single Movement
With an item properly labeled, the next crucial step is nailing down your documentation process. Every single action, from moving an item out of intake into storage, to transferring it between departments, to sending it out for analysis, must be meticulously recorded. This creates an unbroken, chronological history of everyone who has handled the item. Part of building this framework involves understanding concepts like What is IT Asset Disposition (ITAD), which is fundamentally built on secure tracking and handling.
Key Takeaway: Your documentation is your proof. If an action is not logged with a date, time, and signature, it essentially never happened in the eyes of an auditor or a court.
To maintain this integrity, your documentation has to capture very specific data points every time the item changes hands or location.
For any chain of custody log to be considered reliable, it must include a few critical pieces of information. The table below breaks down the essential data points that form the backbone of a defensible audit trail.
Essential Chain of Custody Documentation
| Data Point | Description | Importance |
|---|---|---|
| Unique Identifier | The barcode or case number assigned at intake. | Guarantees the item is tracked consistently throughout its lifecycle. |
| Handler Information | The name and signature of every person who handles the item. | Establishes personal accountability for each transfer of custody. |
| Date and Time Stamp | The exact date and time of every transfer or action. | Creates a precise, chronological timeline of the item’s journey. |
| Location Tracking | The specific location where the item is stored or moved. | Prevents items from being misplaced and confirms secure storage protocols. |
| Condition Notes | Any observations about the item’s condition upon transfer. | Documents the item’s integrity and flags any potential tampering or damage. |
Capturing this level of detail is what makes a chain of custody truly defensible. It transforms a simple log into a powerful accountability tool. Automating this process with the right software, like our Enasys Asset Tracking Software, can dramatically reduce manual errors and keep your audit trail pristine.
Controlled Transfer and Secure Storage
Finally, you need to define ironclad transfer and storage protocols. Transfers between personnel or departments are where the chain of custody most often breaks. Standardize this process by creating designated, secure hand off zones and requiring both parties to sign off on the transfer log in real time. No exceptions.
When it comes to storage, the solution has to match the sensitivity of the items. For high value assets or critical evidence, evidence lockers provide individual, auditable security. For larger inventory or bulk items, wire security cages create a secure, access controlled environment that prevents any unauthorized contact. These physical barriers are not just suggestions; they are integral components that enforce your procedures and protect your assets from tampering, damage, or theft.
Choosing the Right Physical and Digital Tools
A strong chain of custody framework is only as good as the tools you use to enforce it. The right equipment and technology are what transform your policies from a document in a binder into a living, breathing system of accountability. This is where you bridge the physical world of your assets with the digital world of tracking to build a modern, resilient system.
The goal here is to create layers of security. Physical measures give you that immediate, visual confirmation of an item’s integrity, while digital tools provide an automated, real time audit trail that takes human error out of the equation.
Fortifying Security with Physical Solutions
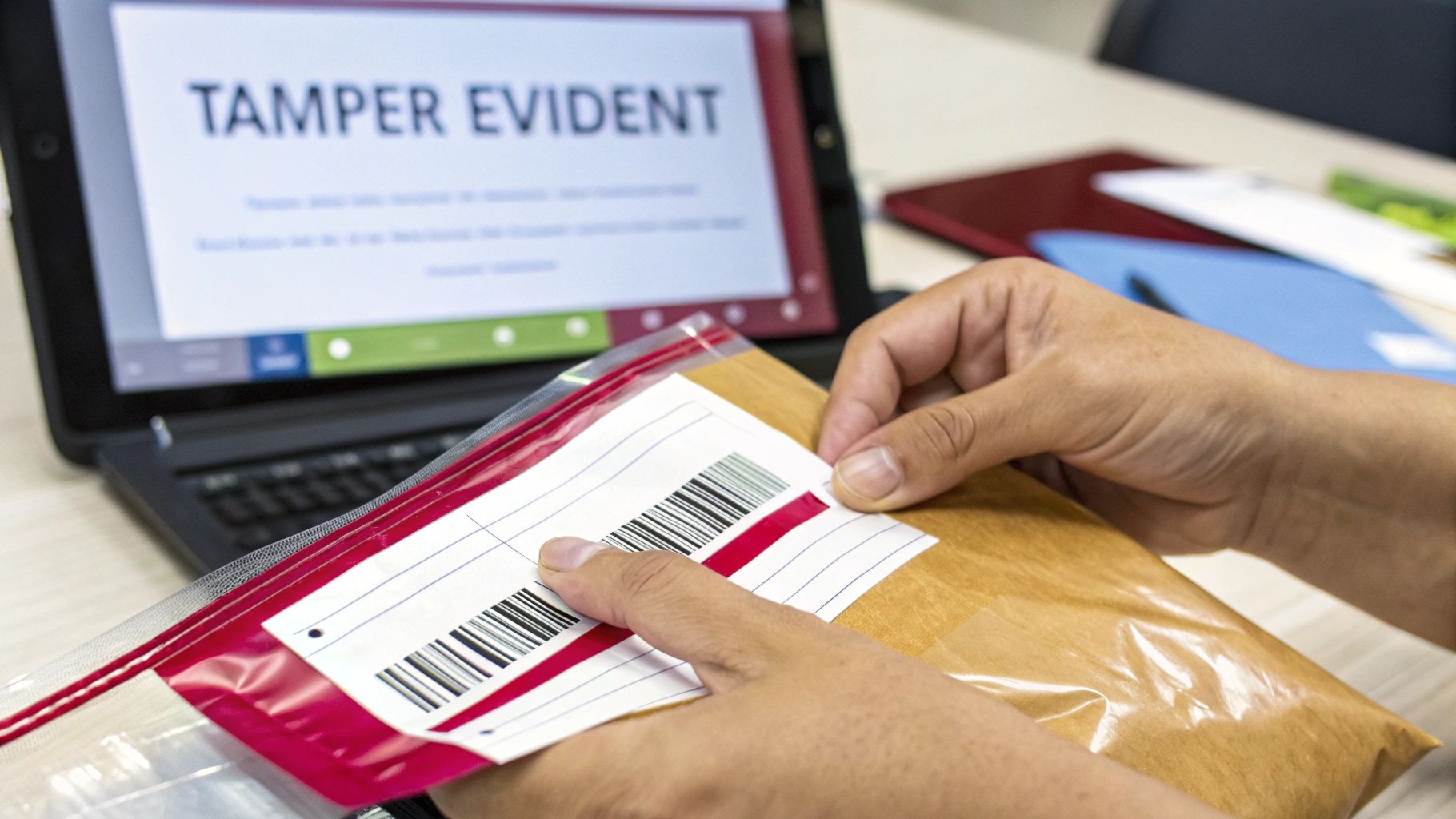
Physical security starts with tamper evidence. It is your first line of defense. Tamper evident seals and bags provide an instant, undeniable visual cue if an item has been compromised. Unlike a standard container, these products are designed to show irreversible proof of entry, like a broken seal or a “VOID” message that appears on the surface.
This simple technology is incredibly powerful. It deters unauthorized access and gives handlers a clear, immediate way to verify an item’s integrity at a glance.
Pro Tip: When choosing tamper evident bags, match the bag’s features to the item’s needs. For sensitive documents, a simple adhesive seal might do the trick. For biological samples or critical evidence, look for bags with unique serial numbers and tear off receipts to strengthen your documentation trail.
Beyond seals, controlling the environment itself is critical. Secure wire partitions create a formidable barrier for larger assets or bulk storage areas. They allow for visibility while strictly controlling access, ensuring only authorized personnel can enter designated zones. When combined with other physical measures, they form a comprehensive security ecosystem. For more information on specialized secure storage, explore our complete line of evidence storage solutions.
Integrating Digital Tools for Accuracy
While physical security prevents unauthorized access, digital tools are essential for creating an accurate, automated audit trail. This is where barcode scanners and Radio Frequency Identification (RFID) technology come into play. Integrating these tools into your procedures drastically reduces the manual data entry that so often leads to mistakes.
Instead of relying on handwritten logs that can be messy and hard to read, a quick scan of a barcode or an RFID tag instantly updates an item’s status in your central tracking system. This captures crucial information with near perfect accuracy:
- The exact time of the scan
- The location of the scanner
- The ID of the operator performing the scan
This automation does not just improve accuracy; it also saves a ton of time, freeing up your team to focus on handling assets carefully rather than getting bogged down in paperwork. The result is a clean, reliable, and highly efficient digital record of every single touchpoint.
Creating a Hybrid Security Ecosystem
The most robust chain of custody procedures do not rely on just one type of tool. They create a hybrid ecosystem where physical and digital solutions work together, covering all potential vulnerabilities.
Think about a practical scenario: a sensitive lab sample arrives at your facility.
- Physical Intake: The sample is immediately placed in a tamper evident bag with a unique serial number and barcode.
- Digital Logging: That barcode is scanned, which logs the sample into your inventory system, automatically recording the time, date, and receiving personnel.
- Secure Storage: The sealed bag is then placed inside a locked evidence locker or within a secure wire partition. Access to this area is also logged digitally.
- Auditable Trail: Every time the sample is moved or accessed, its barcode is scanned, and the physical tamper evident seal is visually inspected.
This layered approach ensures you have both a physical deterrent against tampering and a precise digital record of every movement. Combining these tools creates a system that is not only secure but also easily auditable, providing a powerful defense of your procedures.
Making Chain of Custody Work for Your Industry
Chain of custody is not a rigid, one size fits all checklist. While the core principles of documentation, security, and accountability are universal, how you apply them depends entirely on your world. The system that works for a warehouse moving consumer electronics will utterly fail a forensic lab handling DNA evidence.
To build a process that actually works, you have to tailor it to your specific operational environment. This means getting real about your industry’s unique challenges and deploying the right equipment to head off those risks. Let’s look at how these principles play out in three completely different, high stakes environments: law enforcement, healthcare, and logistics.
Law Enforcement: When Evidence Integrity is Everything
For police departments and crime labs, the stakes could not be higher. A single gap in the chain of custody can get evidence thrown out of court, torpedoing an entire case. The biggest threats are cross contamination and tampering, precisely what defense attorneys are trained to find. Every single handover, from the crime scene to the evidence room to the lab, has to be documented perfectly.
This is not a job for standard issue cabinets. It demands specialized equipment built for absolute integrity. Our evidence lockers are purpose built for this exact scenario. Many feature pass through designs, allowing an officer to securely deposit evidence on one side without ever gaining access to the main evidence room on the other. This creates a secure, single point of transfer that makes the chain of custody ironclad.
Other mission critical features include:
- Individually Keyed Compartments: This isolates every piece of evidence and restricts access only to authorized custodians.
- Ventilated Options: Absolutely essential for properly drying biological evidence to prevent it from degrading.
- Durable Steel Construction: It is a simple but formidable physical barrier against any unauthorized access attempt.
Healthcare: Protecting Samples and Patient Privacy
In a hospital or lab, the focus shifts to patient confidentiality, sample integrity, and airtight regulatory compliance, especially with HIPAA. A mislabeled blood vial or a tissue sample stored at the wrong temperature is not just an error, it can lead to a devastating misdiagnosis. The chain of custody here protects both the physical sample and the sensitive patient data attached to it.
The main risks are misidentification, biological contamination, and data breaches. To fight this, healthcare facilities need versatile, secure storage. Our modular casework offers configurable, non porous surfaces that are easy to sterilize, which is a huge advantage in reducing contamination risk. And for moving samples between wings? Secure, lockable medical carts are non negotiable. They ensure samples and patient files are shielded during transit, maintaining a secure chain from the bedside to the lab.
Key Takeaway: In healthcare, chain of custody is just as much about protecting patient privacy as it is about preserving the physical sample. The right equipment helps enforce both at the same time.
Logistics: Locking Down High-Value Inventory
For warehouses and distribution centers, chain of custody is all about loss prevention. High value goods like electronics, pharmaceuticals, or luxury items are constant targets for internal theft and shrinkage. The real challenge is maintaining a detailed audit trail in a high volume, fast paced environment with countless touchpoints, from the receiving dock to the shelf to the outbound truck.
The biggest risks are theft, misplacement, and damage. Here, tough physical security is your best friend. Industrial shelving keeps inventory organized for clear visibility and efficient tracking, while heavy duty wire security cages create secure, access controlled zones for your most valuable goods. These cages are a powerful physical deterrent, limiting access to a handful of trusted personnel and creating a controlled area where every entry and exit is logged.
The pharmaceutical supply chain is a perfect example of why this matters. Substandard and falsified medicines are a global problem, often stemming from weak links in the supply chain. As documented by the NIH, rigorous chain of custody, from sample purchasing to lab analysis, is critical for post market surveillance that keeps contaminated products off the shelves. You can learn more about how chain of custody helps ensure pharmaceutical safety.
Ready to design a secure system that meets your industry’s specific demands? Request a Quote today for a free, no obligation layout and see how our competitive pricing can benefit you.
Common Chain of Custody Mistakes and How to Avoid Them
Even the most buttoned up framework can have weak spots. All it takes is a single oversight in your chain of custody procedures to call everything into question, whether it is evidence for a major case, a high value product in your warehouse, or a critical lab sample. The first step to building a truly resilient system is knowing where things usually go wrong.
These are not just minor clerical errors; they are vulnerabilities that can lead to massive financial losses, legal nightmares, and a damaged reputation. The good news? Most of these mistakes are entirely preventable with the right training, tools, and a bit of foresight.

Incomplete Documentation During Handoffs
One of the most frequent, and damaging, errors happens during transfers. It is the moment the chain is most likely to snap.
What Went Wrong: An employee is moving a box of sensitive components to another department. They are in a rush, so they get a quick “got it” instead of a signature on the log. Later, when items from the box are missing, there is no paper trail. No proof of who had it last. It is a huge accountability gap that is impossible to close.
Proactive Solution: You have to make real time sign offs mandatory for every single transfer. Period. Implement digital logs with barcode scanners to make it fast and foolproof. For high value assets, create designated, camera monitored hand off zones and give staff secure, lockable transfer carts to protect everything in transit.
Vague or Improper Labeling
If an item is not labeled correctly from the get go, the integrity of its entire journey is compromised. Ambiguity is the enemy of a secure chain of custody.
What Went Wrong: A lab technician gets a new batch of samples and labels them with just the project name, forgetting to add unique identifiers. Down the line, two samples from that same project look identical. It becomes impossible to tell them apart, rendering both useless and wasting a ton of time and resources.
Proactive Solution: Your labeling protocol needs to be non negotiable. Every item gets a unique serial number or barcode at intake, no exceptions. The label must include the date, time, and the handler’s initials. Using durable, pre serialized labels from our shipping supplies ensures consistency and kills the temptation for on the fly mistakes. This simple step removes all the guesswork.
Key Insight: To get ahead of common chain of custody mistakes, especially those tied to identity fraud or tampering, think about adding another layer of verification. For instance, implementing biometric security measures can ensure only authorized individuals handle or transfer your most sensitive assets.
Neglecting Regular Audits
Just assuming your procedures are being followed without ever checking is a recipe for disaster. Complacency is how even the best designed systems fall apart.
What Went Wrong: A company has a great chain of custody manual gathering dust on a shelf. No one has audited the process in over a year. During a surprise regulatory inspection, it is discovered that employees are taking shortcuts, logs are spotty, and secure storage areas are often left unlocked. Now, the company is facing stiff penalties and scrambling to fix a broken system.
Proactive Solution: Schedule regular, and unannounced, audits. This keeps everyone on their toes and ensures protocols are followed day in and day out, not just when someone is watching. This has become even more critical in our digital age. With global cyberattacks surging by 38% in 2022, the proper handling of digital evidence is paramount. As forensics experts will tell you, without meticulous documentation, even the most compelling digital evidence can be thrown out. A simple checklist can help you spot weaknesses long before they become liabilities.
Your Partner in Building an Unbreakable Chain of Custody
At the end of the day, a rock solid chain of custody is not just about ticking boxes on a form. Think of it as a strategic asset, your frontline defense against costly mistakes, legal headaches, and damage to your reputation. It all boils down to a blend of meticulous documentation, robust physical security from quality materials, and the right technology to connect the dots. When you get this right, you are not just protecting assets; you are protecting your entire operation.
That is where we come in. At Material Handling USA, we do not just sell products; we deliver the peace of mind that comes from a system you can actually trust. We stake our reputation on quality, competitive pricing, and getting you what you need faster than anyone else in the business.
We know that no two operations are the same. A police evidence room has different demands than a pharmaceutical lab or a distribution center. That is why we are ready to help you design a secure system that fits your exact workflow and space with our free layouts and designs.
Ready to build a truly unbreakable chain of custody? Let’s talk. Our experts are on hand for a free, no obligation consultation to map out the layouts and designs that will work for you.
Let’s build a secure solution together. Request a Quote online or Call (800) 326-4403 to speak with a specialist today.
Common Questions About Chain of Custody
When you are in the trenches, trying to get a chain of custody system running smoothly, the big picture policies are one thing, the practical, day to day questions are another. Managers often wrestle with the same challenges: where do things usually go wrong, how can we make improvements without a huge budget, and how do we keep the system from falling apart over time?
Let’s tackle some of the most common questions we hear from folks on the ground.
Where Do Chains of Custody Most Often Break Down?
Without a doubt, the single weakest link in any chain of custody is human error during a handoff. It is the moment of transfer where everything can go wrong. A signature gets missed on a log, someone is in a hurry and does not wait for confirmation, or an item is moved without being documented at all. These are not malicious acts; they are just small oversights that can completely invalidate your entire process.
Your best defense is to make the right way the only way. Using tools like secure evidence transfer lockers or lockable carts builds the process right into the workflow. It forces a deliberate, documented action, which dramatically cuts down on the chance of an unrecorded exchange.
Key Takeaway: Transfers are your highest risk moments. You need to fortify them with mandatory, real time documentation and physical security tools that ensure every handoff is captured, every single time.
How Can We Improve Our Procedures on a Tight Budget?
You do not need a six figure budget to make a real difference. In fact, some of the most effective improvements are surprisingly low cost. If you are working with limited funds, start with the essentials that give you the biggest bang for your buck.
Implementing simple tools like tamper evident labels and serialized logbooks is a fantastic first step. For a minimal investment, you get instant visual verification of tampering and a much stronger paper trail. Once that is in place, you can look at phasing in bigger ticket items. Even affordable equipment like basic security shelving can be a cost effective way to better organize assets and secure your storage areas.
How Often Should We Audit Our Chain of Custody Procedures?
Think of audits as preventative maintenance. If you wait until there is a problem, it is already too late. Regular audits are absolutely non negotiable for catching protocol decay before it becomes a real liability.
We strongly recommend conducting thorough internal audits every quarter. In between those, mix in random, unannounced spot checks. This keeps everyone on their toes and ensures the procedures are being followed consistently, not just when they know an audit is coming.
During these checks, zero in on a few critical areas:
- Logbook Accuracy: Are all the fields filled out? Are the signatures, dates, and times all there and correct?
- Physical Security: Walk the floor. Check the locks on doors, security cages, and lockers. Are seals and tamper labels intact?
- Protocol Adherence: The best way to do this is to simply watch a few transfers happen. Are people actually following the steps you have laid out?
Catching a small deviation early stops it from becoming a bad habit across the whole team. A proactive audit schedule is not about catching people out, it is about keeping your entire chain of custody strong and legally defensible.